Fostering a Culture of Safety in Healthcare
Alert Media
JUNE 14, 2022
The post Fostering a Culture of Safety in Healthcare appeared first on AlertMedia.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Alert Media
JUNE 14, 2022
The post Fostering a Culture of Safety in Healthcare appeared first on AlertMedia.

NexusTek
OCTOBER 13, 2021
Cybersecurity as a Matter of National Security. Business security, energy security, food security…national security. government, a ransomware attack threatened food security of people in the Midwest. national security. Healthcare Ransomware 8. October 13, 2021. All one in the same.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Reciprocity
SEPTEMBER 30, 2022
Data breaches against healthcare organizations affected more than 1 million people in 2020. The average total data breach cost in the same year was far higher in the healthcare industry ( $7.13 As one can see, the healthcare industry is one of the most attractive targets for cyber attackers and data thieves.

Solutions Review
OCTOBER 20, 2023
Additionally, it’s all too common for IT leaders to lose sight of the big picture while heads down at work, which increases the risk of being slow to respond and unprepared to get back up and running in the event of a security crisis. Opt for secure storage of local backups on portable hardware-encrypted external devices.
Advancing Analytics
OCTOBER 4, 2023
Since Hydr8’s inception in 2017 our goal has always been to streamline the implementation of a secure, robust, and scalable Data Lakehouse platform and to expedite extracting value from data for our customers. Our inclusion in this program is testament to our fantastic engineering teams' hard work in achieving this goal.

Solutions Review
OCTOBER 20, 2023
Additionally, it’s all too common for IT leaders to lose sight of the big picture while heads down at work, which increases the risk of being slow to respond and unprepared to get back up and running in the event of a security crisis. Opt for secure storage of local backups on portable hardware-encrypted external devices.

Business Resilience Decoded
OCTOBER 19, 2023
In this episode, we are joined by Dr. Bernard Jones, professor of homeland security and emergency management at St. Throughout his career, he’s worked in several industries, including tech and data, healthcare, security, and higher education. John’s University. John’s University.

Online Computers
OCTOBER 28, 2023
Backup media Backup media are the physical or digital storage devices used to store duplicate copies of data. These media serve as secure repositories for backed-up information. Differential backups can be faster to restore from than incremental backups.

Solutions Review
JANUARY 25, 2024
They explore the challenges we face in safeguarding digital identities, the emerging threats to our online spaces, and the innovative strategies being developed to secure personal information against unauthorized access. This is likely to impact industries where transparency matters, such as healthcare, financial services, and insurance.
Emergency Planning
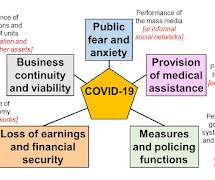
MARCH 11, 2020
US Homeland Security Council 2005, UK Government 2008), while in others it did not. US Homeland Security Council 2005. It is now more than ten years since there was a general push to induce countries to plan for pandemics (WHO 2005). In some quarters, it had an immediate effect (e.g., Spinney, L. Jonathan Cape, London, 352 pp.

Emergency Planning
AUGUST 20, 2021
In Haiti, a third of the population lacks secure access to food. Fortunately, despite continual disruption of healthcare, the effect of Covid-19 has so far been limited (600 deaths in a population of 11.5 Consider, for example, the role of the Internet and social media. The outbreak killed 9,000 Haitians and infected 800,000.

Solutions Review
FEBRUARY 1, 2024
They explore the challenges we face in safeguarding digital identities, the emerging threats to our online spaces, and the innovative strategies being developed to secure personal information against unauthorized access. This is likely to impact industries where transparency matters, such as healthcare, financial services, and insurance.

Solutions Review
JANUARY 18, 2023
Erich Kron is a Security Awareness Advocate at KnowBe4 and is a veteran information security professional with over 25 years of experience in the medical, aerospace manufacturing and defense fields. Erich Kron, KnowBe4. Headquartered in Boston, Mass., RackTop Systems. When: Thursday, January 26, 2023, at 12:00 PM Eastern.

Solutions Review
JANUARY 28, 2024
They explore the challenges we face in safeguarding digital identities, the emerging threats to our online spaces, and the innovative strategies being developed to secure personal information against unauthorized access. This is likely to impact industries where transparency matters, such as healthcare, financial services, and insurance.

Solutions Review
APRIL 21, 2022
Physical security is about keeping your facilities, people and assets safe. Unfortunately, all the firewalls in the world can’t help you if an attacker removes your storage media from the storage room.). Securing your company’s employee passwords will protect your internal data from being accessed by an outside source.

Behavior Group
APRIL 22, 2019
Cybercriminals Continue to Succeed, data breach, cybersecurity, cybercriminals, cyberattacks, cisos From social media, hospitality, healthcare and even mail delivery, 2018 proved that there is no escaping cybersecurity flaws, regardless of the type of business or its popularity. For… Continue reading.

Solutions Review
JANUARY 25, 2023
As part of Data Privacy Week (January 22-28) we called for the industry’s best and brightest to share their Identity Management , Endpoint Security , and Information Security comments. Business leaders should also increase the capabilities required for digital trustworthiness whether it is privacy protection or data security.

Online Computers
JULY 22, 2022
For example, if you're in the healthcare industry, you'll want an IT partner that understands things such as Health Insurance Portability and Accountability Act (HIPAA) compliance and how to keep protected health information secure. This is to ensure you avoid the risk of noncompliance and other industry-specific security threats.
Pure Storage
MAY 20, 2024
In fact, the US Cybersecurity & Infrastructure Security Agency (CISA) advises victims not to pay ransomware attackers, noting that in many cases the hackers will demand more money or often target the same organization again. Even then, cybercriminals may not return control to the organization they’ve targeted.

Reciprocity
APRIL 4, 2022
No lock has ever been invented that was completely secure; if an intruder is determined to get in, he or she can usually find a way. Digital risk protection solutions are critical for today’s security teams and risk management processes- especially when the average cost of a data breach now tops $4.2 Third-Party Risk.

Pure Storage
MARCH 23, 2022
bn) will be from the consumer and media sectors. Wider use cases will involve everything from healthcare to smart utilities. Making data governance and security strategic priorities to drive customer trust and safeguard your business. And only a fraction of these gains (£9.4 add link to previous blog].

Fusion Risk Management
MARCH 4, 2022
Many organizations are noticing a multiple-folds increase in scanning attempts; few others, specifically healthcare services, reported an uptick in phishing emails. Below are some best practices and considerations for organizations to stay secure. According to President Biden’s State of the Union address last week, the U.S.

Reciprocity
NOVEMBER 5, 2021
The Center for Insurance and Policy Research addresses seven types of cyber liability insurance: Liability for security or privacy breaches. Business interruption costs and extra expenses related to a security or privacy breach. These coverages can help to protect the company from the costs associated with a security breach.

Pure Storage
DECEMBER 21, 2023
High performance, reliability, and scalability are key considerations for storage solutions, along with addressing expanding data needs for compliance, privacy, security, cost, and location. Data protection with built in Security. To access and process large video files efficiently, businesses need low-latency storage.

Reciprocity
AUGUST 15, 2022
But as more companies use technology across all parts of the enterprise and more compliance requirements focus on cybersecurity, IT security is becoming an increasingly central part of the CMS. Compliance regulations for financial institutions differ from compliance in healthcare , so it’s crucial to understand the applicable laws.

Advancing Analytics
MAY 23, 2022
Facial recognition and retina scanning are also helping financial institutions to improve security procedures and therefore reducing fraud. The use of computer vision applications for healthcare is often regarded as a turning point in medical image processing and diagnosis. HEalthcare. Source: New York Times. Manufacturing.

Solutions Review
JULY 21, 2023
On-Demand: Solutions Review Hosts Rubrik for Exclusive Spotlight Webinar With the next Solutions Spotlight event , the team at Solutions Review has partnered with leading zero trust data security vendor Rubrik. Read on for more. And now that Rubrik is partnered with Microsoft, its Microsoft 365 protection is even stronger.

Solutions Review
MARCH 31, 2023
Jonathan Halstuch, Chief Technology Officer and co-founder of RackTop Systems If you are protecting data with backups, you also need to secure it “Organizations have been using backups as a strategy to recover data and prevent total data loss in the instances of a critical system failure or natural disaster.
Marketpoint Recall
FEBRUARY 10, 2020
Throughout late January, state media outlets proclaimed confidence in how Xi Jinping was handling the outbreak and offered assurances that the epidemic would be ultimately resolved under the leadership of CCP. However, Chinese state media coverage has subsequently downplayed or totally ignored this admission.
Plan B Consulting
MAY 10, 2023
The company has a significant presence across various industries, including: government, healthcare, local authorities, finance, telecommunications, and transportation. Capita provides cyber services as it mentions on its website “Providing robust, effective, and scalable security solutions”.

Reciprocity
DECEMBER 19, 2022
Thanks to social media, word of a business breaching a code of conduct or misbehaving can spread quickly. Or if you’re a healthcare provider offering tele-medicine and accepting credit card payments, you need to implement controls protecting both electronic personal health information (ePHI) and cardholder information.

Managecast
MARCH 27, 2020
According to Naked Security, “It’s all relative of course, but downplaying it might be to miss the point because this attack was unusual in another way – officials said it coincided with a disinformation campaign carried out via SMS, email and social media that reportedly claimed that a national quarantine of the US was imminent.”

Reciprocity
MARCH 28, 2022
Factor analysis of information risk (FAIR) provides a common risk mitigation vocabulary to help you to address security practice weaknesses. Security-savvy people and organizations will stick with you if they know you’re working hard to protect their data and security. As your organization grows, its risks will change.

Solutions Review
SEPTEMBER 27, 2021
The platform automatically screens and continuously monitors third-party risks against the world’s largest risk intelligence database, over 500 regulatory lists, 200,000 unique media publications, 1.5 million politically exposed persons, and more than 8 million adverse media profiles. StandardFusion. Platform: StandardFusion.

Erwood Group
FEBRUARY 4, 2024
Automated Incident Response: How it Works: AI-driven incident response systems can automatically detect and respond to security incidents. Natural Language Processing (NLP) for Communication Analysis: How it Works: NLP processes and analyzes natural language data, including emails, social media, and news articles.

Reciprocity
AUGUST 18, 2022
Factor Analysis of Information Risk (FAIR) provides a common risk mitigation vocabulary to help you to address security practice weaknesses. For example, a company focusing on payment systems may comply with the PCI DSS standard to secure credit card information. As your organization grows, its risks will change. Risk Identification.

Pure Storage
OCTOBER 19, 2023
Top among those challenges is the need to select the right data architecture and supporting technologies to meet evolving business needs and data requirements while ensuring data quality, security, and more. Business units or teams own specific data collections and have responsibility for the quality, accessibility, and security of that data.

Reciprocity
APRIL 4, 2022
In security, risk assessments identify and analyze external and internal threats to enterprise data integrity, confidentiality, and availability. A risk analysis is conducted for each identified risk, and security controls are pinpointed to mitigate or avoid these threats. Each component comprises several necessary actions.

Reciprocity
AUGUST 17, 2022
Make a security risk assessment and a prudent decision. For any risk assessment to succeed, the person conducting the assessment should understand the risk being examined: financial, compliance, security, operational, and so forth. For instance, emergency services or healthcare professionals may employ dynamic risk evaluations.

Reciprocity
MARCH 24, 2022
Concerns over information security and data privacy are driving this change, but so are laws. It encompasses controls for cybersecurity, information technology, data security, and business resiliency. For these, you may request evidence of the vendor’s own risk management, information security, and regulatory compliance efforts.

Reciprocity
AUGUST 24, 2022
After acceptable risk levels have been established, evaluate vendors’ security performance — and if a vendor’s cybersecurity is too lax for your tastes, require that vendor to make improvements as necessary. Therefore, you need to monitor its security often, if not constantly. Security patch management. Compliance.

Reciprocity
OCTOBER 1, 2022
Also known as web-based software, hosted software, or on-demand software, SaaS liberates organizations from the often complex tasks associated with software and hardware management, as the SaaS provider manages access to the application, including security, availability, and performance. GRC Software Solutions.

Reciprocity
DECEMBER 27, 2022
GRC is an integrated approach to managing the organization’s governance, IT and security risks, and regulatory compliance functions. This engenders trust, strengthens its competitive position, and protects company assets from security breaches, data losses, and financial penalties. What Is GRC? Clear Organizational Hierarchy.

Plan B Consulting
JANUARY 9, 2022
Today I’m going heavy-duty and writing the bulletin about the media response of Amedia AS, a Norwegian print and internet news organisation. Amedia AS are the largest publisher of local media in Norway. The first mention of the National Security Authority. Who are Amedia AS?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content