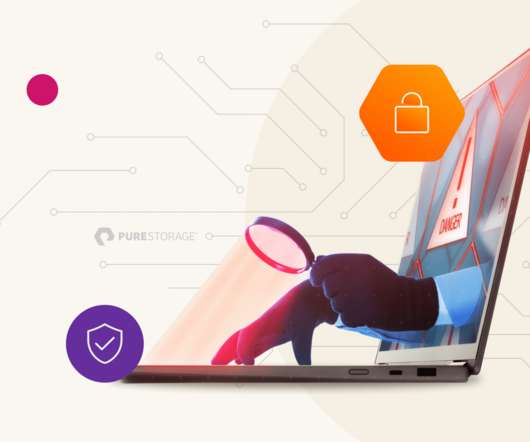
What is Zero Trust Architecture?
Pure Storage
MAY 2, 2024
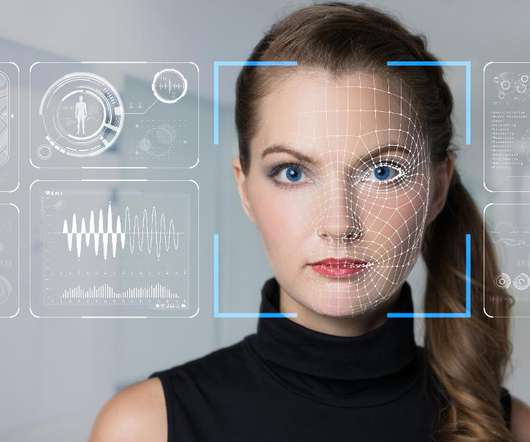
In this article, we’ll discuss what ZTA is, why it’s augmenting traditional perimeter network security, and how to implement it. Every user and system, regardless of their location, must authenticate and validate their identity before accessing network resources. Implement least privilege. Assume a breach will occur.









































Let's personalize your content