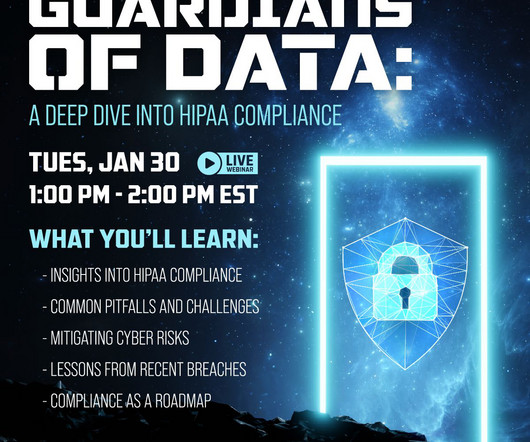
Guardians of Data: A Deep Dive into HIPAA Compliance
Online Computers
JANUARY 8, 2024
Join us for a concise webinar where we'll share actionable insights to enhance your cybersecurity resilience: Employee Training: Educate staff on identifying and mitigating common cybersecurity risks. Security Audits: Conduct routine audits to address vulnerabilities and prevent unauthorized data access.





























Let's personalize your content