How Zerto Helps State, Local and Education Solve and Scale Data Protection
Zerto
JULY 25, 2023
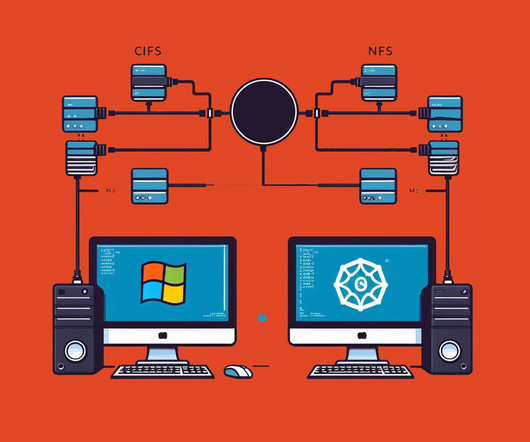
IT professionals serving state, local and education entities have a tremendous responsibility. Tasked with keeping data protected from bad actors while ensuring IT systems operate without disruption is not for the faint of heart. Seeking help planning or updating your data protection strategy?
















Let's personalize your content