The Blurred Lines of Data Sovereignty: Do You Really Own Your Data?
Pure Storage
FEBRUARY 21, 2024
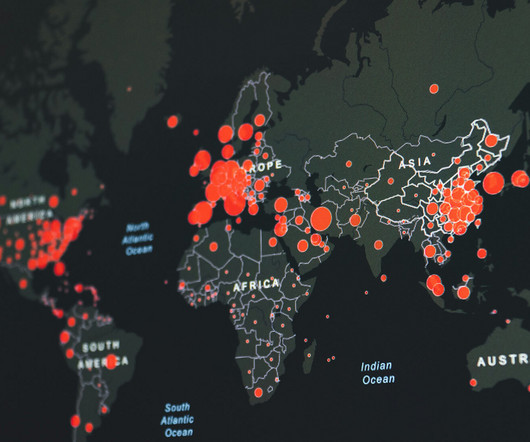
The Impact of Data Sovereignty on Business Data sovereignty compliance can be a major factor in decisions on data management, data security, data residency, and even IT architecture and cloud vendor selection. Simply moving data across borders can entail extra processes that impede the seamless flow of data.













Let's personalize your content