Book Review: Case Studies in Disaster Recovery
Recovery Diva
APRIL 12, 2023
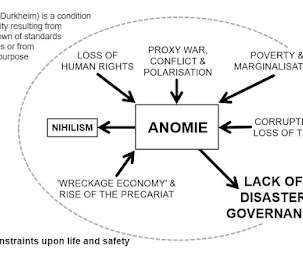
However, it is also constrained by the community’s resource availability, adaptability, and existing vulnerability among other things. and government (a critique of FEMA disaster assistance programs).




















Let's personalize your content