15 Backup and Disaster Recovery Best Practices to Consider
Solutions Review
FEBRUARY 23, 2024
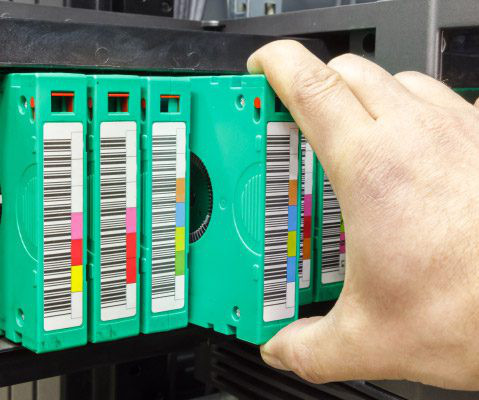
Backup and disaster recovery (BDR) strategies are of paramount importance to enterprises due to their critical role in preserving data integrity, ensuring business continuity, and mitigating risks associated with various disruptions. Evaluate the impact of different disasters on your business operations.






















Let's personalize your content