The Four Phases of Disaster Recovery
MHA Consulting
SEPTEMBER 14, 2023
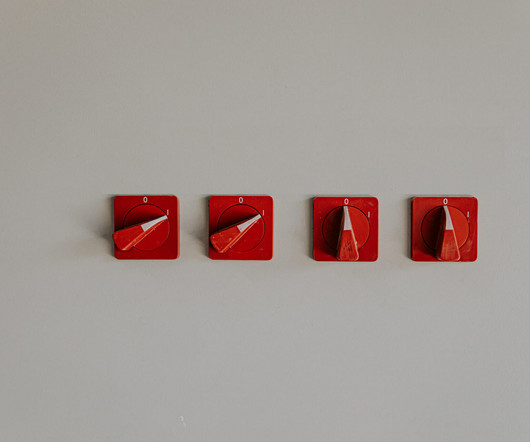
In today’s post we’ll look at why organizations still need to be adept at IT disaster recovery (IT/DR) and describe the four phases of restoring IT services after an outage. Phase 1: Preparation Technically, preparation is not a phase of disaster recovery since it happens before the outage. Let’s look at them one by one.
















Let's personalize your content