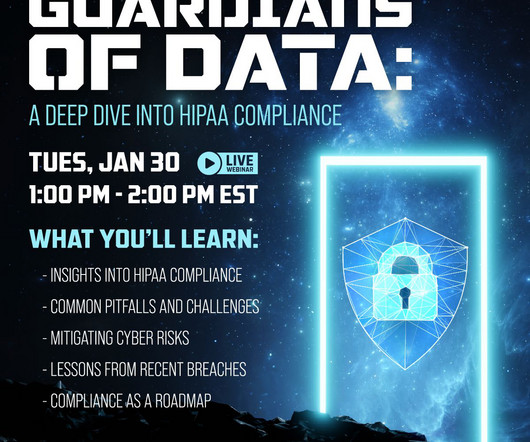
Guardians of Data: A Deep Dive into HIPAA Compliance
Online Computers
JANUARY 8, 2024
Security Audits: Conduct routine audits to address vulnerabilities and prevent unauthorized data access. Incident Response Plan: Develop an effective plan aligned with HIPAA regulations to respond swiftly to security breaches.





















Let's personalize your content