How to Put CISA’s “Shields Up” Recommendations Into Action
Pure Storage
MARCH 7, 2022
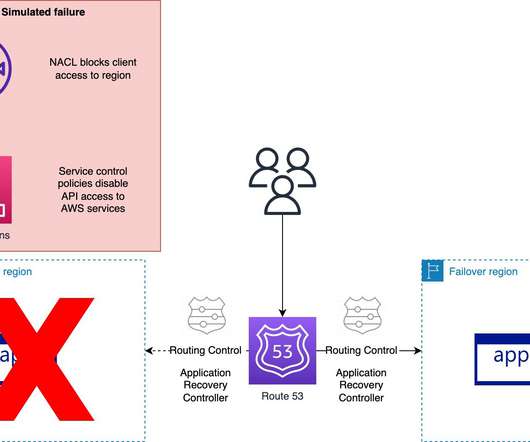
This means being proactive with plenty of hurdles like multifactor authentication and admin credential vaulting. Know your tolerance for downtime, create a regular cadence for testing backups, and have plans for getting mission-critical data back online, such as a bunkered backup architecture or staged recovery environment.














Let's personalize your content