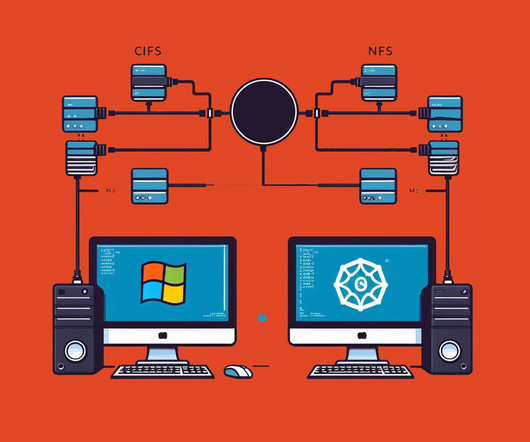
CIFS vs. NFS: Which Filesystem Is Right For Your Needs?
Pure Storage
NOVEMBER 29, 2023
Two prominent file-sharing protocols, Common Internet File System (CIFS) and Network File System (NFS), play pivotal roles in enabling smooth data exchange. This article explores CIFS and NFS, their functionalities, differences, performance, administration, and best use cases for enterprise data management professionals.












Let's personalize your content