Acronis Cyberthreats Report Year-end 2022: Data under attack
Acronis
DECEMBER 19, 2022
Today we published the Acronis Cyberthreats Report: Year-end 2022, highlighting our findings from the back half of the year.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Acronis
DECEMBER 19, 2022
Today we published the Acronis Cyberthreats Report: Year-end 2022, highlighting our findings from the back half of the year.
Emergency Planning
AUGUST 3, 2023
This document was first published in 2008 and has been updated (somewhat irregularly) at roughly two-year intervals. b) In terms of its methodology, the NRR discusses vulnerability but does not accept the premise (Hewitt 1983) that it is the major component of risk.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Recovery Diva
OCTOBER 13, 2021
Publisher : Routledge – Taylor & Francis Group, New York and London. The editors are experts in the field with many years of conducting research and teaching with particular emphasis on social vulnerability and cultural complexity within the context of emergencies and disasters. link] April 2020.

Recovery Diva
MAY 7, 2022
Book Review: The Invention of Disaster: Power of Knowledge in Discourses of Hazard and Vulnerability. Publisher : Routledge by Taylor and Francis Group London and New York. Labeling certain groups as vulnerable justifies the intervention of outside actors (i.e. Series Editor: Ilan Kelman. For more information: [link].

Castellan
JUNE 29, 2022
Article Originally Published on Forbes in May 2022. Proactive Treatment Of Vulnerabilities. In your role as a board member or a member of your organization’s leadership team, it is your job to set and inspect the organization’s overall vision while also steering the company toward a sustainable future.

Solutions Review
JULY 14, 2023
Product enhancements will include additional automation and the use of AI to help identify digital footprint vulnerabilities and optimize the ability to remove those exposures. In fact, the response has helped begin shaping Solutions Review as a premier enterprise technology publishing platform. Read on for more. Read on for more.

Recovery Diva
APRIL 12, 2023
Publisher: Butterworth-Heinemann, Elsevier, Oxford, UK and Cambridge, Massachusetts, USA. However, it is also constrained by the community’s resource availability, adaptability, and existing vulnerability among other things. Volume Editor: Jane Kushma, Ph.D. December 2022. Paperback ISBN: 9780128095744 eBook ISBN: 9780128095362.
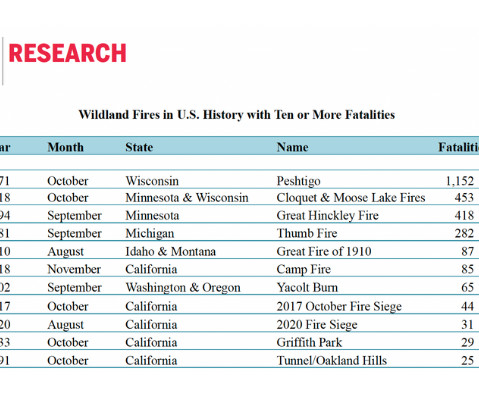
National Fire Protection Association
SEPTEMBER 11, 2023
The fire underscores global concerns about fire and life safety, particularly among developing nations and areas where housing pressures create additional risks for the poorest and most vulnerable populations. The following blog was originally published October 8, 2021.

Castellan
AUGUST 5, 2021
Article Originally Published on Forbes in August 2021. “The shutdown of such a vital pipeline, one that has served the East Coast since the early 1960s, highlights the vulnerability of aging infrastructure that has been connected, directly or indirectly, to the internet,” the New York Times reported.

IT Governance BC
JANUARY 12, 2021
After all, it’s only once you’re aware of the ways you’re vulnerable that you can put appropriate defences in place. Additionally, its integrated risk, vulnerability and threat databases eliminate the need to compile a list of potential risks, and the built-in control sets help you comply with multiple frameworks.

Solutions Review
OCTOBER 13, 2023
Cloudflare Helps Discover Major Online Vulnerability This global vulnerability gives attackers the ability to generate attacks larger than anything the Internet had seen before. This ensures a unified user experience for Acronis-owned and integrated applications, enhancing efficiency and reducing errors. Read on for more.

Emergency Planning
FEBRUARY 8, 2023
Source: Wikimedia Commons An interesting map was published by the US Geological Survey shortly after the Turkish-Syrian earthquakes. [1] Most of them are highly vulnerable to seismic forces. the 'violent' level. [2] Many, perhaps most, people in Turkey live in multi-storey, multiple occupancy reinforced concrete frame buildings.

Crisis Response Journal
OCTOBER 16, 2012
In the next issue of Crisis Response Journal (Volume 8, issue 2 - published this week) Emily Hough examines how reliance on now-common technology could well have created even greater vulnerability in a crisis

everbridge
AUGUST 24, 2022
Everbridge partner Atos , a global leader in cloud and the digital workplace, recently published an interesting take on the future of work and how new technology trends will impact businesses and employees alike, now and in years to come. Protect against individual online vulnerability. SCHEDULE DEMO.

National Center for Disaster Prepardness
OCTOBER 23, 2023
We were also stunned by the sense of extraordinary vulnerability to unknown forces that had also hit the Pentagon and had likely targeted the nation’s Capital. And do something to make our nation and the world less vulnerable. We felt naked and unprepared in the face of terrorism at a scale never before seen in the U.S.

Solutions Review
JUNE 23, 2023
Top Storage and Data Protection News for the Week of June 23, 2023 New Arcserve Survey Reveals Ransomware and Data Recovery Vulnerabilities The segment focuses on government IT departments’ approach and experience with ransomware and data recovery preparedness.

National Fire Protection Association
JUNE 21, 2023
The NFPA Journal article Strength in Numbers, which was recently published in the Summer 2023 issue, reinforces this point, showing that the number of mass shootings in the U.S. Webber recommends conducting risk-based assessments to better understand and address existing vulnerabilities. “Do And we’re going in the wrong direction.”

Solutions Review
SEPTEMBER 21, 2023
Arcserve Drops New Research on Healthcare Data Protection The findings reveal gaps, vulnerabilities, and misconceptions in the healthcare sector, potentially hindering its ability to effectively safeguard and recover data in the event of malicious attacks and accidental data outages stemming from human error or natural events.

Plan B Consulting
MAY 15, 2023
In a scenario where the attacker can afford to operate quantum computers, but the victim cannot, this presents a significant vulnerability to an organisation’s cyber-security. Furthermore, any lost encrypted data would now have to be assumed to be unencrypted.

Pure Storage
JULY 12, 2023
This doesn’t particularly mean that the open access is a security vulnerability since both resources are using key-based authentication. product publisher = data.cbs_azure_plans.azure_plans.plans[0].publisher publisher version = data.cbs_azure_plans.azure_plans.plans[0].version Unless you get those keys, you cannot authenticate.

Recovery Diva
JUNE 30, 2022
Publisher: University of Texas Press Austin Texas. already set by the degree of vulnerability and marginalization existing in disaster-impacted communities. Professor Emeritus of Sociology and American. Studies, Yale University and Lori Peek, Professor of Sociology and Director of the Natural. Hardcover Price $90.00.
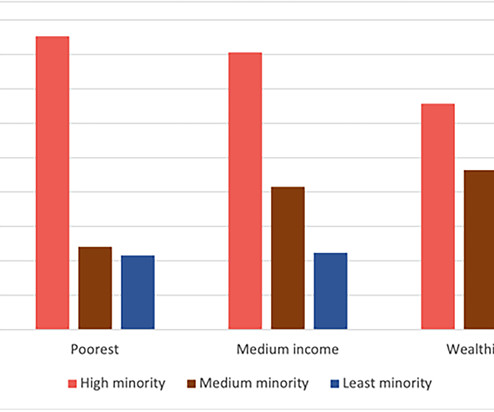
National Center for Disaster Prepardness
MARCH 27, 2023
Similarly, a study published by the Rockefeller Foundation found that areas with a high ‘minority’ population share were more than four times as likely to suffer a blackout compared to predominantly White areas. Of those cases, 42% were children, who are more vulnerable to CO poisoning due to their higher metabolic rates.

Pure Storage
DECEMBER 14, 2021
We have to assume they’ll use every tool, skill set, and vulnerability they can to keep their revenue streams healthy. Building access systems have already been in the sightlines of hackers, and security professionals have already pointed out serious vulnerabilities in smart building control systems that hackers could exploit.

Security Industry Association
SEPTEMBER 9, 2022
Public space is more vulnerable to a myriad of threats posed by commercial drones. Over a year later, the current administration published a national action plan this April concerning domestic counter-unmanned aircraft systems (CUAS). The first-person view capability is a great example. The plan provides eight key recommendations.

Security Industry Association
FEBRUARY 15, 2023
This could compromise not only our physical security posture, though our systems, but entire organizational networks through gaps and vulnerabilities left on the physical security system side. So the question is, what can we do to help reduce this risk?

LogisManager
SEPTEMBER 24, 2021
It’s no question that they’ve got a lot to share, so we’ll be publishing these insights to our blog to help you make more informed business decisions. Companies have continued to fall victim to risk management failures stemming from third-party vulnerabilities.

MHA Consulting
JANUARY 26, 2023
Then as now, the government published resources to help organizations protect themselves. Many BCM consulting firm sites publish blogs, white papers, and webinars on BC topics that are available free to all comers or in some cases free with registration. BCM consultancy websites. Collectively these are an exceptional resource.

Fusion Risk Management
SEPTEMBER 14, 2023
While these include technical capabilities such as network security, they should also involve awareness training across your organization to ensure that each member of your team is playing a part in minimizing your vulnerabilities to cyber threats.

LAN Infotech
JANUARY 29, 2022
The Federal Trade Commission (FTC) recently published a new safeguards regulation incorporating most of the recommended revisions to the 2002 GLBA guidelines for safeguarding client information, on 10th January 2022. Risk assessment is meant to evaluate possible vulnerabilities to client data that might result in an illegal breach.
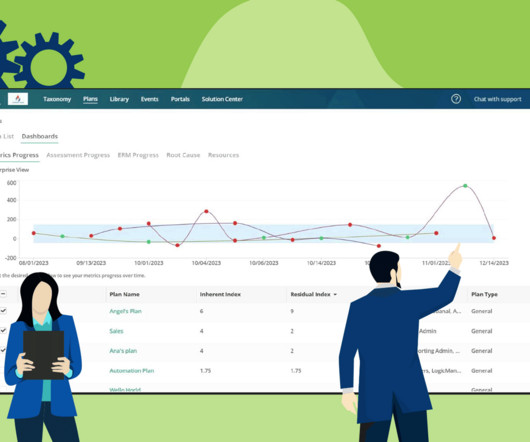
LogisManager
DECEMBER 12, 2023
Empowering Strategic Decision-Making with Real-Time Risk Dashboards Published: December 12, 2023 In LogicManager’s latest product update release, powerful new in-app visualizations enable real-time data analysis, fostering informed decision-making and proactive risk strategies for strong corporate governance.

Online Computers
JANUARY 20, 2022
Nonprofits, in particular, are as vulnerable to operational disruptions as for-profit businesses. An example of this is when an organization publishes and disseminates one be-all mobile number for all types of communications. Related article: How to update your disaster recovery plan.

Plan B Consulting
NOVEMBER 3, 2017
The National Audit Office investigation into the “WannaCry cyber attack and the NHS” was published this week, so I thought I would share 10 lessons from the report which are relevant to all organisations. Unless your systems are patched and up-to-date, you are vulnerable to an attack. This is basic IT management!

Plan B Consulting
NOVEMBER 3, 2017
The National Audit Office investigation into the “WannaCry cyber attack and the NHS” was published this week, so I thought I would share 10 lessons from the report which are relevant to all organisations. Unless your systems are patched and up-to-date, you are vulnerable to an attack. This is basic IT management!
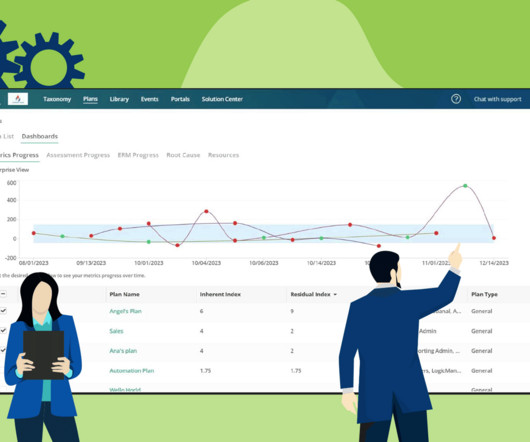
LogisManager
DECEMBER 12, 2023
Empowering Strategic Decision-Making with Real-Time Risk Dashboards Published: December 12, 2023 In LogicManager’s latest product update release, powerful new in-app visualizations enable real-time data analysis, fostering informed decision-making and proactive risk strategies for strong corporate governance.

LogisManager
MAY 9, 2023
To better understand your risk management program’s vulnerabilities and areas that need improvement, take the Risk Maturity Model Assessment. With ERM it is a straightforward exercise to combine the job of vendor due diligence and the job of security access rights reviews to reduce costs without creating vulnerabilities.

Emergency Planning
MAY 30, 2019
These may be published separately in an academic journal. At Risk: Natural Hazards, People's Vulnerability and Disasters (2nd edition). The document is decanted from many different studies, some of which have been commissioned specially for it. An example of this for the 2013 GAR can be found in Di Mauro (2014). GAR Distilled.

Security Industry Association
NOVEMBER 9, 2021
Hackers have studied these systems, identified vulnerabilities, and created exploits that are simple, inexpensive and fast. This sensitive data and the vulnerable way it is being transmitted requires attention. And if a system is vulnerable to attack, it is just a matter of time before it is targeted. ×10 38 combinations.
National Center for Disaster Prepardness
MAY 13, 2020
As the world scrambles each week to grapple with the seemingly insurmountable number of positive cases and deaths from the COVID-19 pandemic, public policy is failing some of America’s most vulnerable communities. Although COVID-19 has been called the “great equalizer” on different media platforms , the data tell a different story.

Pure Storage
FEBRUARY 9, 2024
For instance, a study by Backblaze, a cloud storage provider known for publishing hard drive reliability statistics, has shown that SSDs generally exhibit lower annualized failure rates (AFR) than HDDs. These components make HDDs more vulnerable to physical damage and wear over time, complicating upgrades and replacements.

FS-ISAC
SEPTEMBER 8, 2021
The related controls and processes for handling vulnerabilities are quite similar. FMIs such as EBA CLEARING are already subject to unified standards under the European Central Bank’s (ECB) Cyber Resilience Oversight Expectations (CROE) published in December 2018.

Security Industry Association
SEPTEMBER 26, 2022
Over a year later, in April 2022, the current administration published a national action plan concerning domestic counter-unmanned aerial/aircraft systems (CUAS). The plan provides eight key recommendations. So, what about the private sector and venues that host large public events? Over the past several years, the U.S.
Solutions Review
OCTOBER 27, 2023
But, with the digital landscape changing and with the introduction of new methodologies like DevOps, open-source adoption, and the shift towards hybrid cloud solutions, prioritizing mainframe vulnerability management is more important than ever. Read on for more.

everbridge
JUNE 16, 2022
Preparedness is key because it helps you identify vulnerabilities and coordinate how you might best protect your colleagues, customers, partners, and organization in a crisis. The preparation stage is when you’ll assemble your core crisis team. Rice University in Houston has a ready answer: Everbridge.

Fusion Risk Management
MARCH 14, 2022
And in the 10 months since we’ve published the policy, we have seen that borne out. Some of the world’s most significant websites becoming unavailable and worrying vulnerabilities arising that may have been exploited by malicious actors. That future proofing element is vital because you can’t always predict what is going to happen.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content