What is internet security?
Acronis
JULY 15, 2022
Internet security is an umbrella term used to describe the multitude of tactics used to protect a consumer and safeguard the activities and transactions they conduct over the internet.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Acronis
JULY 15, 2022
Internet security is an umbrella term used to describe the multitude of tactics used to protect a consumer and safeguard the activities and transactions they conduct over the internet.

The Rand Blog
AUGUST 29, 2023
The use of internet-based platform services like Amazon, DoorDash, and Uber Eats is increasing and can be helpful. Some form of centralized policy action may help; local governments could play a more-active role. But the companies that offer these services may be engaging in predatory practices that can harm users and local businesses.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Acronis
FEBRUARY 7, 2023
Today, February 7th, is Safer Internet Day, created in an ongoing effort to combat potential malicious online activity facing the average connected user. While the internet can be a valuable educational resource, it can also be a fertile breeding ground for criminal activity.
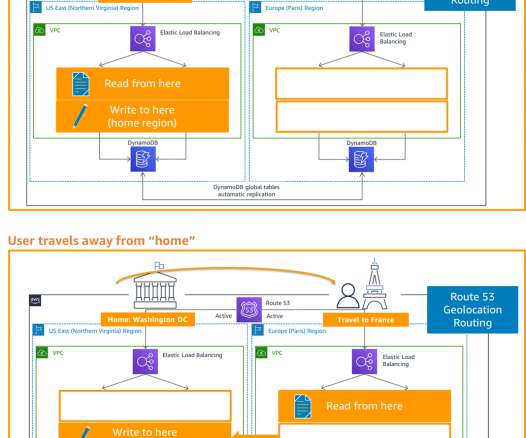
AWS Disaster Recovery
JUNE 23, 2021
My subsequent posts shared details on the backup and restore , pilot light, and warm standby active/passive strategies. In this post, you’ll learn how to implement an active/active strategy to run your workload and serve requests in two or more distinct sites. DR strategies: Multi-site active/active. DR strategies.
Behavior Group
MAY 11, 2017
Physical Security, information security, cybersecurity, privacy The physical security space is changing, with emerging threats, new criminal techniques, terrorism and hostile activism just of few of the drivers of change. The post The Internet of Things Invades Physical Security appeared first on Behaviour Portugal.

Emergency Planning
MARCH 29, 2023
lifts [elevators] blocked: people possibly trapped in them trains stranded: people possibly stranded in them traffic control inoperable: possibility of accidents and queues at road junctions critical facilities (hospitals, police stations, etc.)

Citrix
JUNE 21, 2022
The growth in Internet of Things (IoT) devices has been tremendous over the last 10 years, with an estimated 10 billion to 15 billion IoT devices active as of 2022. Every major industry either actively uses or is considering … The post Scaling IoT solutions with Citrix ADC first appeared on Citrix Blogs.

Bernstein Crisis Management
OCTOBER 20, 2022
Successful organizations adapt to the world around them, and with a general public that’s more aggressive in sharing negative opinions, and FAR more able to engage in that sharing thanks to the epic double-edged sword we call the internet, it seems to me that it’s time we all accept this trend isn’t going to reverse any time soon.

Security Industry Association
APRIL 1, 2024
Each year, the conference tackles the issues that matter most to young professionals in the security industry and features a diverse array of premier learning sessions, interactive workshops and lively activities geared toward rising stars in the industry. This year, we’re excited to host AcceleRISE in D.C.,

Erwood Group
JANUARY 3, 2023
The dark web is an unindexed part of the internet. Though not all sites on the dark web are for criminal activity, It’s a key area of the world wide web for criminals and illegal activity, making it attractive to people who want to keep their identities and data secure from others. More on that later.

Plan B Consulting
FEBRUARY 13, 2024
It was unexpected that many more hadn’t explored or at least experimented with the technology, endeavouring to comprehend its relevance to our profession and activities. At its current stage, AI reminds me of the early days of the internet, characterised by dial-up connections and limited information access.

FS-ISAC
SEPTEMBER 15, 2023
One of my main duties included briefing the Commander on the latest research/threat intel on cyber domain adversary activity. I quickly realized I had trained him to ‘go to his happy place’ and ignore me because I was briefing him on generic threat activity so it was not anything he would ever make a decision on.

Online Computers
NOVEMBER 30, 2023
Be careful about sharing personal information online While sharing information is essential for many online activities, such as creating social media profiles or making online purchases, it's crucial to be mindful of what you disclose and to whom. Activate multifactor authentication for an extra security layer.

Security Industry Association
MAY 30, 2023
Efforts like these would not be possible without the support and active participation of our member volunteers. We encourage interested SIA members to contribute their passion and expertise by getting involved in our standards committees, groups and activities.” Version 2.2.1

Pure Storage
JUNE 12, 2023
The Internet Assigned Numbers Authority (IANA) assigns default ports, but an application can configure any port when it installs on a computer. For example, if you integrate it with Active Directory, you need port 389 opened. Oracle incorporates LDAPS into its Oracle Internet Directory (OID) service.

Business Continuity Today
JUNE 7, 2022
The mobile device-enabled Augmented Reality(AR) in conjunction with the Internet of Things(IoT) is changing the face of disaster management. AR and IoT technologies are active topics in emergency and disaster response. AR and IoT technologies are active topics in emergency and disaster response.

Security Industry Association
AUGUST 10, 2023
After the 2018 tragedy in Parkland, Florida, the company focused its efforts on the commercial school security market to tackle the growing active shooter problem. I decided to take action and develop a locking system that was the strongest, most integrated device for home use. And what makes your offerings or your company unique?

Zerto
OCTOBER 20, 2022
As we continue with our third and final blog in this series on managing cyberthreats, we’ll explore frameworks from the National Institute of Standards & Technology and Center for Internet Security, which together provide time-tested knowledge and best practices used to combat ransomware. National Institute of Standards & Technology.

Security Industry Association
MARCH 19, 2024
Since the invention of the internet, there has not been a new technology that has captivated its audience as quickly as AI. Threat Detection and Mitigation When it comes to detecting threats, AI supports security efforts by analyzing patterns and identifying unusual activities that may lead to potential problems.

MHA Consulting
OCTOBER 5, 2023
Related on MHA Consulting: Mark My Words: Commonly Confused Business Continuity Terms Two Fundamental Terms One of the most common BC-related internet searches is by people trying to learn the difference between business continuity and IT disaster recovery. Sometimes the form business continuity management (BCM) is used.

Business Continuity Today
JUNE 7, 2022
The mobile device-enabled Augmented Reality(AR) in conjunction with the Internet of Things(IoT) is changing the face of disaster management. AR and IoT technologies are active topics in emergency and disaster response. AR and IoT technologies are active topics in emergency and disaster response.

Bernstein Crisis Management
OCTOBER 1, 2022
Sure the excuse of, “I’m not an internet person” may have worked ten years ago, but it can only harm your business today. If you simply don’t have time to stay active on multiple social media accounts that’s fine, but you need to own your profiles and have alerts for new messages or interactions delivered to an email you check regularly.

Online Computers
OCTOBER 7, 2021
This can reveal the victims’ interests and activities, such as if they’re involved in activism or charity works, or if they actively participate in political message boards. To do all of these, you must monitor your internet traffic for web exploits and utilize web logging to spot and stop suspicious activities.

Security Industry Association
OCTOBER 21, 2022
She is a 22-year veteran of Intel with deep technology expertise across the Internet of Things, AI, physical security and cybersecurity, data center and storage. Additionally, Hanson is a Distinguished Fellow for the Innovation Institute for Fan Experience and was named the No. 3 IFSEC Global Security Influencer in 2021.

Pure Storage
JANUARY 21, 2022
It may sound obscure to the non-developer, but Log4j is actually one of the most widely used pieces of open source code on the internet. The Java-based code, developed under the Apache Software Foundation, does what it sounds like it does: It logs an application’s activity as entries in a record.

Fusion Risk Management
SEPTEMBER 15, 2021
If you are reading this, then you have Internet access. In this day and age, pretty much everyone from kids to employees not only have Internet access, but cannot make it through the day without that continual access. In fact, only 51% of new viruses introduced on the Internet are picked up by anti-virus solutions on day 1.

Online Computers
NOVEMBER 2, 2021
Your internet connection at home is a potential gateway for hackers to illegally access your data. They can tap into your internet provider in order to snoop in or steal your data. A VPN keeps hackers and snoops from spying on your online activities, allowing you to browse the internet safely.

Security Industry Association
FEBRUARY 22, 2024
Access control Fire alarm Surveillance systems Nurse call and patient wandering Internet of Things and smart city technology Mass notification Intrusion detection systems Door hardware Safes and vaults What’s something we might not know about your company – or something new you’re doing in security?

Security Industry Association
MARCH 13, 2024
The advisory board provides prescriptive guidance and advocacy for new and existing cybersecurity strategies and solutions, which enables SIA to prepare its members for challenges related to wider adoption of the Internet of Things and the use of secure networked devices for security.

Zerto
JUNE 7, 2022
A recent IDC report shows that 79% of those surveyed activated a disaster response, 83% experienced data corruption from an attack, and nearly 60% experienced unrecoverable data. Over the past few years, we have seen a large uptick in ransomware and the havoc that it can cause organizations. What is Ransomware? – An Overview.

Security Industry Association
NOVEMBER 9, 2021
The adoption and integration of Internet of Things and Industrial Internet of Things devices has led to an increasingly interconnected mesh of cyber-physical systems that expand the attack surface and blur the once clear lines between cybersecurity and physical security.

NexusTek
AUGUST 15, 2023
Harnessing the global connectivity we now take for granted, the internet of things (IoT) has taken the world by storm, with a multitude of smart gadgets that feed our insatiable hunger for convenience, pique our curiosity about the leading edge of tech, and dazzle us, honestly, just by being plain “cool.”

Risk Management Monitor
JANUARY 27, 2022
However, the algorithms that support them and govern many users’ online activities could end up being something akin to the “pre-cogs” from Minority Report that predict future crimes because the algorithms are collecting so much personal information. Users do not get benefits from people and companies using and profiting off of their data.

Reciprocity
APRIL 4, 2022
More specifically, within digital risk management are the active measures that businesses can take to protect their assets: digital risk protection. DRP is the active piece of the cybersecurity puzzle, and is an imperative for every organization. What is Digital Risk Protection? Digital connections are essential.

MHA Consulting
JULY 27, 2023
Organizations now have to contend with a heightened risk of drought, flooding, heat waves, wildfires, hurricanes, political unrest, global conflict, cyberattack, power outages, active shooters, supply chain disruptions, pandemic, social-media impacts, and all the rest. Operational resilience.

Business Resilience Decoded
APRIL 13, 2023
Things like graffiti, vandalism, or even cracked sidewalks or unkempt landscaping can welcome unwanted activity near your facility. The local climate and weather patterns, access to strong internet and cell phone service, and political risks are all impacted by your geography. Geography can impact potential risks to your organization.
Disaster Recovery Journal
OCTOBER 23, 2020
I was explaining the installation of window breakers and door locks to improve their safety in the event of an active shooter. By way of example, we recently held active shooter training for our emergency response team. Looking back, these were team-bonding activities and happy moments with my son. the Internet of Things â??

BMC
MARCH 31, 2022
Every April, we celebrate Earth Day, and this year, BMC is taking it a step further with a whole month of activities for our inaugural Climate Action Month. These are some of the environmentally responsible activities we’re encouraging among ourselves, and hope you’ll join in, too. And we’re not alone. How much money?

BMC
MARCH 31, 2022
Every April, we celebrate Earth Day, and this year, BMC is taking it a step further with a whole month of activities for our inaugural Climate Action Month. These are some of the environmentally responsible activities we’re encouraging among ourselves, and hope you’ll join in, too. And we’re not alone. How much money?

Security Industry Association
OCTOBER 5, 2023
Monitor networks and devices : Use AI-powered IDS systems and other state of the art security tools to monitor networks and devices for suspicious activity. Introduction Pauline Norstrom, founder and CEO of Anekanta Consulting, serves on the SIA Cybersecurity Advisory Board.
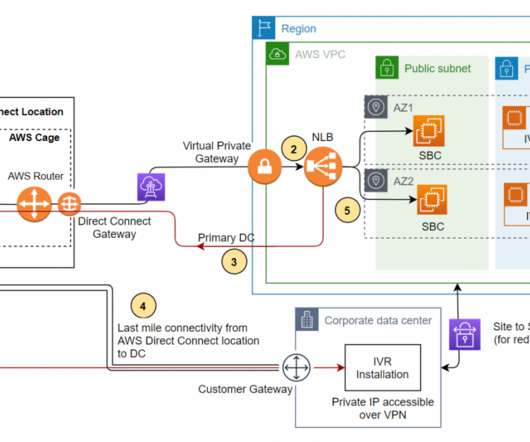
AWS Disaster Recovery
SEPTEMBER 16, 2021
These are backup and restore, active/passive (pilot light or warm standby), or active/active. Make sure that the telecom provider for the SIP trunk is different from the internet service provider (ISP). RPO is the maximum acceptable amount of time since the last data recovery point. Disaster recovery (DR) options.

Online Computers
JULY 14, 2023
If you’re looking for ways to increase the profitability of your New York business, consider using AI and reap the following benefits: Optimized workflows AI enables businesses to automate and streamline various operational processes, leading to enhanced efficiency and productivity that allows employees to focus on higher-value activities.

Online Computers
MARCH 16, 2022
Related article: Practical tips to increase internet speed for your New Jersey office. You can do some spot checking by actively monitoring signal levels using appropriate apps and wireless adapters while walking around. 98 dBm (almost zero noise). A realistic signal for users to have very reliable connectivity would be at ?67

Bernstein Crisis Management
SEPTEMBER 29, 2021
In other words, actively managing their reputation and protecting that 63% of market value from harm! How can you actively build a cushion of goodwill to protect your reputation when it comes under attack? That means your brand becoming the focus of the day’s internet outrage crew – deserved or not!
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content