Ensuring Operational Resilience Amidst Geopolitical Events
Fusion Risk Management
OCTOBER 12, 2023
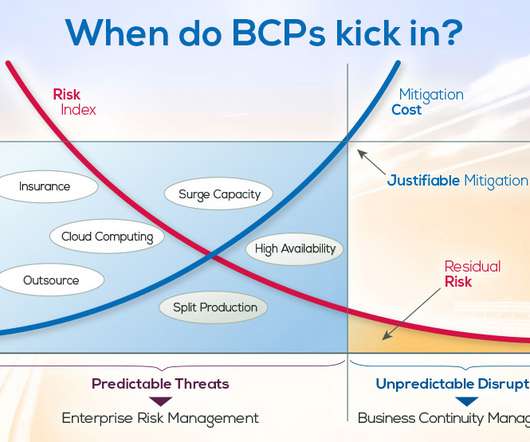
In an increasingly interconnected world, organizations with a global presence face a unique set of challenges when it comes to maintaining resilience during geopolitical events. Crisis and Incident Response Geopolitical events often necessitate the activation of emergency response and crisis response plans.














































Let's personalize your content