How Keeping Track of Microsoft’s Product Plans Can Keep Your Network Secure
LAN Infotech
OCTOBER 17, 2022
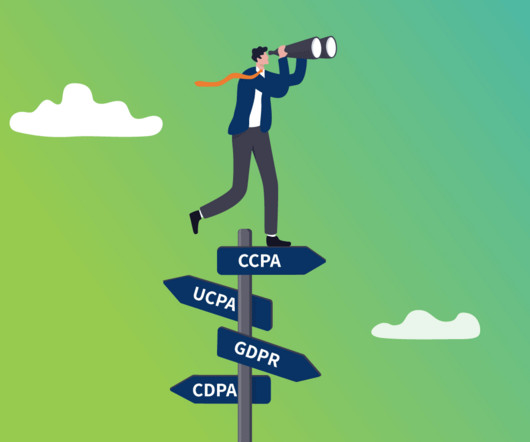
Performing regular network audits, keeping software up-to-date, and keeping abreast of planned software retirements can help businesses and organizations eliminate this source of risk. They can expose their networks to vulnerabilities that hackers and cybercriminals can exploit.















































Let's personalize your content