What is Zero Trust Architecture?
Pure Storage
MAY 2, 2024
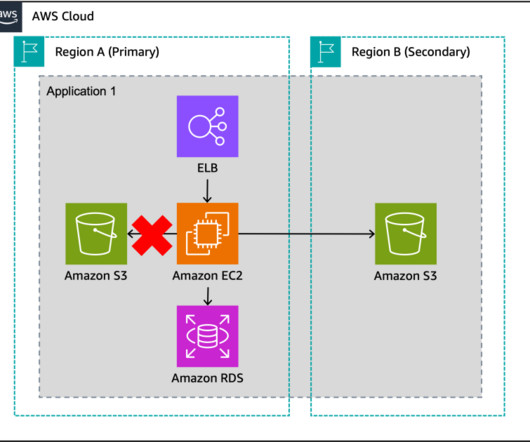
What is Zero Trust Architecture? Why Is Zero Trust Architecture So Important Today? How a Zero Trust Architecture Is Implemented A zero trust architecture (ZTA) is not a catchall in cybersecurity, but it is a vast improvement on traditional network security techniques. In today’s landscape, trust should never be assumed.









































Let's personalize your content