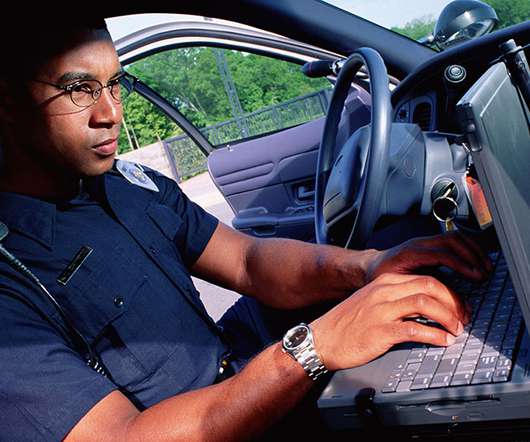
Maryland Set to Enact Nation’s Strongest Regulations for Law Enforcement Use of Facial Recognition Technology
Security Industry Association
APRIL 10, 2024
. – On April 8, 2024, during its last day of regular session, the Maryland General Assembly unanimously passed House Bill 338 / Senate Bill 182 to regulate the use of facial recognition technology by law enforcement across the state, which will now be sent to Gov. Wes Moore for his signature.











































Let's personalize your content